- Sol Oriens, which consults with the federal government on security-related projects including work with the National Nuclear Safety Administration, is REvil's latest ransomware victim.
- Sol Oriens said it became aware of the "cybersecurity incident" in May.
- CNBC has learned that documents posted on the dark web include invoices for NNSA contracts and descriptions of research and development projects managed by defense and energy contractors
The hacker group REvil has become a headache for a new victim: a 50-person firm based in Albuquerque, New Mexico, that consults with the federal government on security-related projects.
Sol Oriens, which consults for the U.S. Department of Energy's National Nuclear Safety Administration, confirmed to CNBC that it became aware of the "cybersecurity incident" in May, its investigation is ongoing and law enforcement has been notified.
Get Southern California news, weather forecasts and entertainment stories to your inbox. Sign up for NBC LA newsletters.
In a statement, the company said it "recently determined that an unauthorized individual acquired certain documents from our systems. Those documents are currently under review, and we are working with a third-party technological forensic firm to determine the scope of potential data that may have been involved."
Mother Jones first reported details of the cyberattack.
Money Report
Sol Oriens did not name the attacker or confirm that it was ransomware, but CNBC has learned that the well-known hacker group REvil was responsible for the assault, according to cybersecurity sources.
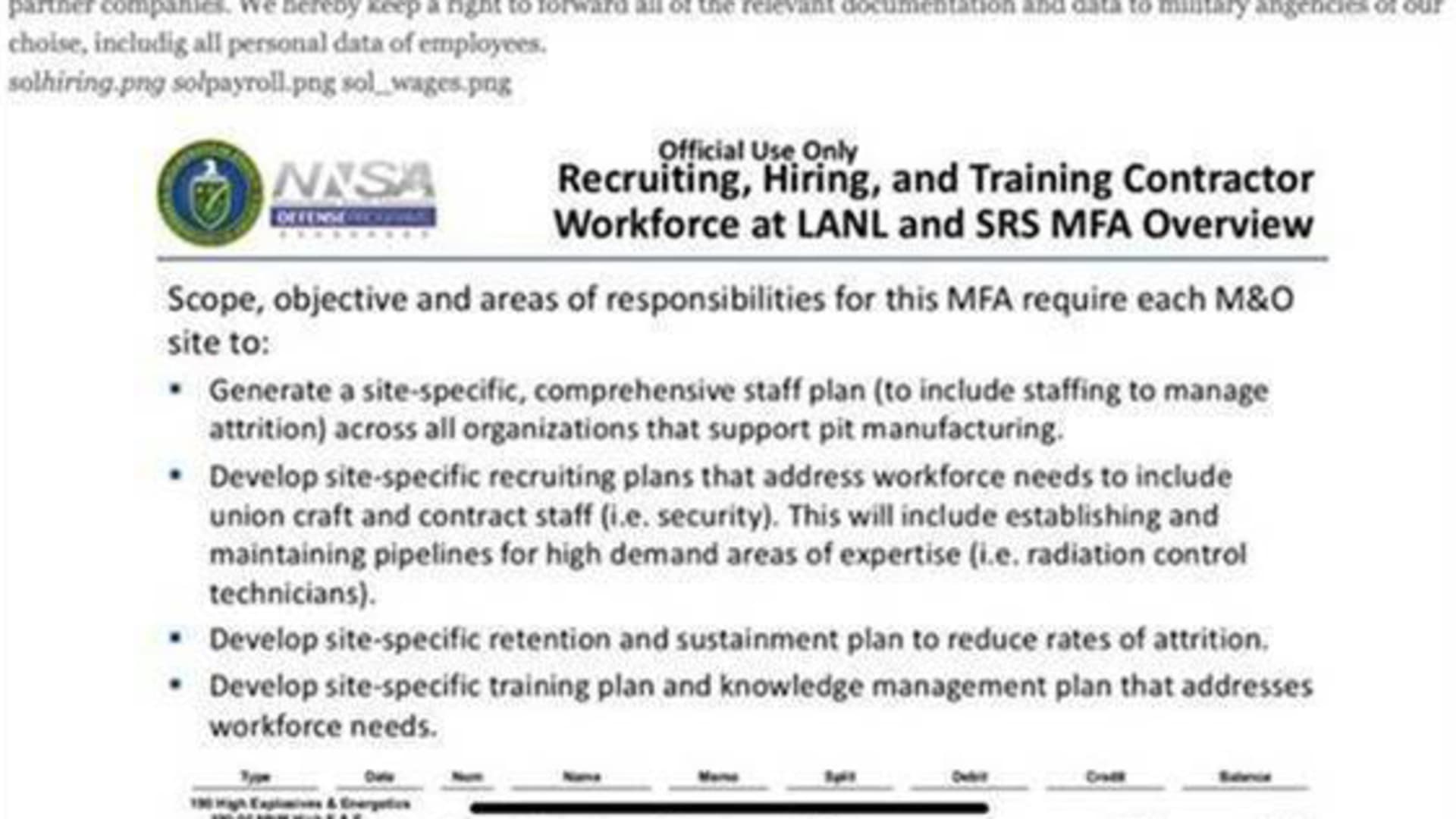
One cybersecurity firm, which has seen documents posted on the dark web, told CNBC that they include invoices for NNSA contracts, descriptions of research and development projects managed by defense and energy contractors dated as recently as 2021, and wage sheets containing full names and Social Security numbers of Sol Oriens employees.
Sol Oriens said that it has "no current indication that this incident involves client classified or critical security-related information." The company declined to say if it paid a ransom to the attackers.
Sol Oriens, describes itself as a technology research and development firm. A recent job posting on GlassDoor, for example, said it was looking for a program analyst who could assist the NNSA with a "complex nuclear weapon sustainment program."
The NNSA, an agency within the Department of Energy, is responsible for maintaining the safety, security and effectiveness of the U.S. nuclear weapons stockpile. It also works with the U.S. Navy on nuclear propulsion, and it responds to radiological emergencies in the United States.
A spokesperson for the Department of Energy declined to comment. A spokesperson for the National Security Council declined to comment.
REvil was most recently responsible for a ransomware attack on JBS, the world's largest meatpacker, which fetched a ransom of $11 million. In April, REvil stole and published blueprints from Apple supplier Quanta Computer. That attack reportedly claimed a $50 million ransom.
"In some ways, Sol Oriens, LLC is just one name among many," a Mother Jones report on the hack said. "There's no indication yet that the company was targeted because of the work it does, rather than just being another potential pay day for hackers."
According to screenshots seen by CNBC, REvil threatened to reveal Sol Oriens' data and documentation on its blog.
Editor's note: An earlier version of this story contained a quote from cybersecurity firm Intel 471. CNBC has since learned that the quote provided by Intel 471, via its outside PR firm CHEN PR, was an excerpt from a story written by Mother Jones' AJ Vicens. CHEN PR confirmed the error to CNBC.
We have corrected the story to accurately reflect the author of the quote, AJ Vicens. We regret the error, and apologize to Mother Jones.